I’ve noticed a regularly occurring email in my inbox: a password reset link sent from Macys.com.
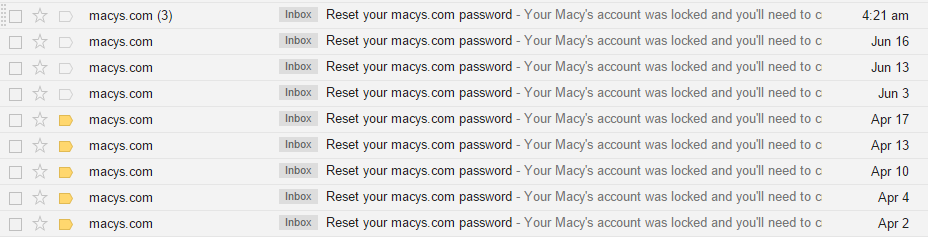
The problem with this? I didn’t try to reset my password! Someone else is requesting a password reset using my email address. But since they can’t actually reset my password this way (since they don’t have access to my email) it’s weird that they would bother, right?
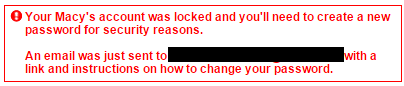
Unfortunately, no, I am still at a disadvantage because of the way Macys.com’s password reset function works. When you attempt to reset a password at Macys.com, you are asked for an email address. When you enter it, you get one of two messages:
1. Email address corresponding to Macys.com account:
“An email was just sent to <email@address.here> with a link and instructions on how to change your password.”
2. Email address not corresponding to a Macys.com account:
“We were not able to locate a Macy’s account associated with that email address. Please try again.”
![]()
The problem with this? This password reset system allows spammers to repeatedly enter emails and have Macys confirm if they belong to a customer. Essentially, bots can use a dictionary-style attack to keep guessing possible email addresses, and Macys.com is nice enough to confirm whether or not it’s a real person’s email. This isn’t good.
This password reset flow allows malicious individuals to build a list of email addresses that are used by everyday people, and spam them. Worse, attackers could focus on trying to guess the passwords for these Macys accounts by repeatedly guessing different possibilities until one worked. This is worrisome since Macys accounts have details like shipping addresses and payment information.
To their credit, it appears that Macys locks a user’s account as part of the password reset function (at least for repeated attempts.) However, this is still a problem for consumers, as as soon as they unlock their account (which they will have to do the next time they shop at Macys.com), bots can once again try to crack their login with a dictionary-style attack.
Macys.com (and the other websites on the web that have a similar vulnerability) should implement a simple fix: serve consumers the same confirmation message when a password reset is requested, regardless if the account exists! Macys.com could serve the following message for password-reset attempts:
“If an account associated with that email address exists, a password reset link has been sent to your inbox.”
…and everyone would be much better off. With this message, an attacker or bot doesn’t know whether the email they input actually belongs to a real person. People wouild be much safer from spam, as well as from brute force attacks against their Macys.com account.
If you know of other sites that have this vulnerability (and I know they exist), please leave a comment on this post. I’m only calling out Macys.com because of the constant password reset links I get in my inbox!

After I registered on macys.com, I start to receive tons of spam on my email address. When I complained about that to them, they did not respond, and the number of spam messages increased dramatically. It seems Macys.com sells their customer database to spammers.
A year and a half later and I’m still getting these inane requests. How many people are giving up their personal info to the spammers behind this? Egads! C’Mon, Macy’s! Get it together!
Getting the same stuff from Bloomingdales now. It’s ridiculous. If I ever purchased from them it had to be years ago. Thanks for this article.
Your advice is Web Security 101. This seems to be getting a fair amount of attention online, so let’s hope they change their messages to users re: validity of account names. However, it did occur to me that the lone message I’ve received about this could have just been Macy’s getting me to visit their site for the first time in 10 years, but I doubt it – that’d generate just as much negative PR.